A Love Letter to OpenClaw
EDITOR'S NOTE
At Patient Zero, we don’t just speculate on AI; we stress-test it in our own lives and workflows. This post by Dan Dekel explores OpenClaw, an open-source framework that represents the "hard-wired" future of AI. While the productivity gains are staggering, the security trade-offs are real. This is the new frontier of Sovereign Engineering.
AI has officially crossed the Rubicon from what AI could do, to what it is already doing. While standard LLMs talk, OpenClaw just does; integrating with everything from my WhatsApp parking bookings to autonomous email orchestration for my holidays.
This is my love letter to OpenClaw. Just kidding. I don't love it that much. But this post is about OpenClaw.
AI's disruptive potential was always something “in the future”, stalled by a hype train that forced us into scepticism and shut downs. OpenClaw has changed the game. It's a rarity: a tool where the reality actually lives up to the expectations.
What is OpenClaw? (The TL;DR)
OpenClaw is just an (open source) program running on your computer. The main thing it does really well, which other agents like Gemini are still not quite good at, is integrate AI with your existing applications. It can read your emails, send WhatsApp messages or launch a web browser and add items to your shopping cart.
Security implications? MASSIVE. More on that later.
Automating the Mundane (Airport Parking)
Take this as an example. I asked OpenClaw to book me a parking spot at the airport. It filled out the form for me:
- Identity - My Name, phone number, email. It knows who I am;
- Context - My flight details. It read my Itinerary from my emails.
- Decision Making - Carbon Offset charge? Nope, it made the decision to skip that (Smart)
The only thing it didn’t know was my car’s rego number, so it sent me a message on WhatsApp asking for it:
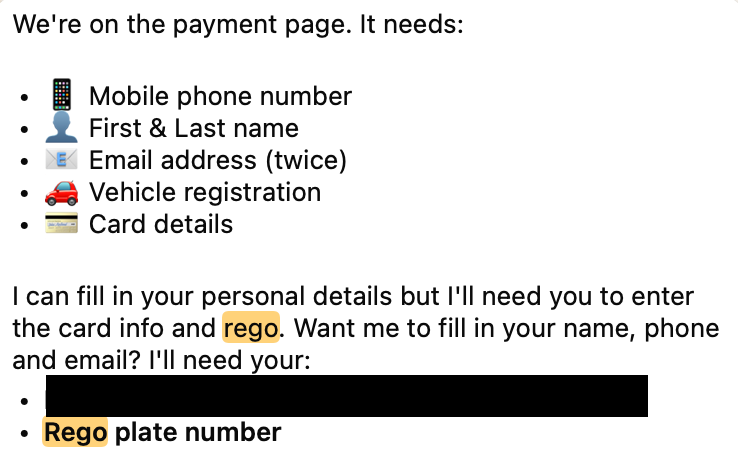
I had the payment page ready for me when I got home (Did I mention I was at Bunnings doing this?).
Payments I still do manually (like a caveman), but probably not for very long.
Verifying the Incompetent: Autonomous Booking Orchestration
Not impressed? Here’s a more complex example.
We have a trip scheduled to Fiji. It was booked by a travel agency (crazy I know). I don’t know what your general perception of travel agents is, but the one we were dealing with were not very competent. In my worry of arriving in Fiji and finding out too late that the travel agency messed up our booking, I asked OpenClaw to confirm directly with the resort the reservation, including dates etc.
So OpenClaw:
- Read my emails and attachments and found out the check-in/checkout dates.
- Searched for the resort’s email online.
- Sent out an email to the resort confirming booking number and dates.
- Monitored my inbox for any replies from the resort.
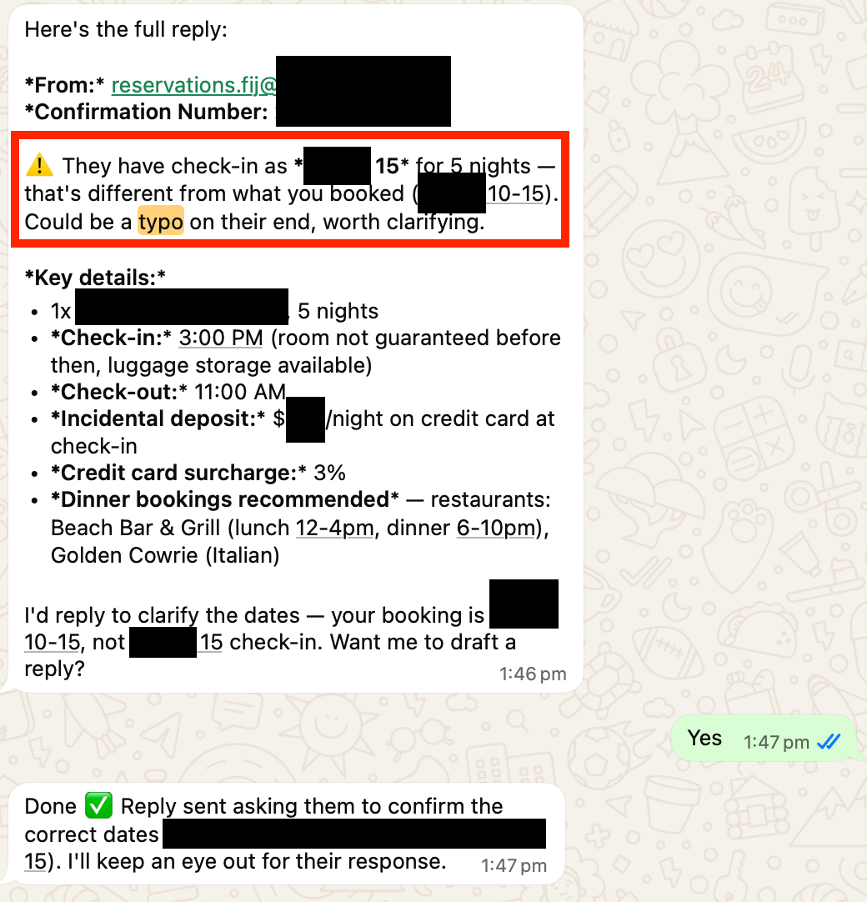
You know what happened next? After a few days OpenClaw sent me this message out of the blue:
OpenClaw: “Good news! The resort replied! 🎉 The check-in dates are different to your booking. Could be a typo on their end, worth clarifying.”
Me: “Yes”
OpenClaw: “Done. Reply sent asking them to confirm the correct dates. I’ll keep an eye on the response.”
It turns out the wrong date WAS a typo by the resort, but I’m glad we checked.
The Security Elephant in the Room
Now, you might be super impressed by all this, but you're probably also wondering how secure this is. The short answer is - you gotta know what you’re doing.
At the time of writing, there's a staggering amount of malicious skills on ClawHub (a public registry for OpenClaw extensions). So that's one thing I tend to avoid.
Furthermore, when I gave OpenClaw permissions to read my calendar or send emails on my behalf I certainly did not check the "Allow all" button. I do have the advantage of understanding what modern OAuth flows require. I understand what I need to do so that OpenClaw does not send my passwords to Anthropic or OpenAI, and I have definitely not relaxed any permissions to “just make it work” (classic IT solution).
The Next Evolution: From .exe to OpenAI
And this is probably the biggest hurdle some users without a tech background will face - they COULD get themselves into a lot of trouble. I like using the analogy of running .exe files in the 90’s:
PC: “Are you sure you want to run this program?"
15 y/o me: “Sure, what’s the worst that can happen?”
There was a reason malware spread so easily in that era.
So, making the experience safe and secure for ordinary users is the next logical step. I would assume that’s probably why the author of OpenClaw has recently joined OpenAI. In his post he says:
“I’m joining OpenAI to work on bringing agents to everyone”
I'm not plugged into the Silicon Valley scene, but my suspicion is this is just the first step in agents becoming mainstream.
Until then, these are still frontier setups. For businesses, the top concerns are AI Security, Governance and, frankly, avoiding misleading* or embarrassing** AI responses to their customers. It takes expertise to build these guardrails, and, if you don’t think you have those skills in-house, I know of at least one company who can help with that.
* Air Canada chatbot misinformation: What travellers should know
** Woolworths AI assistant goes rogue, starts talking about its mother
Deepen Your Sovereign Capability
Don't just watch the AI agent revolution; orchestrate it.
- The Solution: Move beyond "auto-complete" and build autonomous enterprise workflows with App Modernisation & Agentic AI
- The Action: Stop the bleeding on stalled projects and underperforming AI implementations with Project Rescue & Recovery
- The Team: Stop guessing at "prompt engineering" and start building onshore technical muscle with Embedded Software Teams
About the Author: Dan Dekel
Dan Dekel is one of the founders and Co-CEOs of Patient Zero. Passionate about software engineering and AI practices, he bridges the gap between complex architectural theory and the gritty reality of shipping production software.
He believes that true sovereignty requires us to be builders, not just consumers, of technology.